Salamander
- 8 Posts
- 76 Comments

 8·8 days ago
8·8 days agoThank you being around, bringing this nice community here, and helping with the federation!! 😁
Jajaja, sí, soy Mexicano 😁
🥳 Muchas gracias!

 3·9 days ago
3·9 days agoI find it satisfying to see the graph come down :)

 5·9 days ago
5·9 days agoYes, sorry, there was some serious lagg in fetching posts from Lemmy World that persisted for several days and accumulated a 1-week delay.
But after upgrading Mander it is now fetching data from LW quite rapidly and it should be back in-sync in about a day and a half from now.
If you are curious about the ranking algorithm, there is some info here: https://join-lemmy.org/docs/contributors/07-ranking-algo.html

 2·10 days ago
2·10 days agoAmazing work! Thanks a lot!! Took me a few days to get to it but I have upgraded now and it looks great 😄
Awesome! The one with the sustained source loop is my favorite:
Also, the one that shoots out flames paints a picture similar to how a synchrotron behaves, shooting out X-rays into the beamlines as the electron bunches move around.


Upon looking into it closer, the synchrotron is a bit of a mixture of those two concepts - the source loop (booster ring) that is fed by the linear accelerator, and then the larger loop (storage room) that feeds X-rays the beamlines. Of course, many details differ, but still it is interesting to notice the similarities !

 34·3 months ago
34·3 months agoIf the timing is right, I would bring a mushroom grow bag with mushrooms sprouting.
If not… probably my radiacode gamma spectrometer and some of my radioactive items. Maybe a clock with radium painted dials and a piece of trinitite. I think that there are many different points of discussion that can be of interest to a broad audience (radioactivity, spectroscopy, electronics, US labor law story of the radium girls, nuclear explosions, background radiation… etc). As a bonus I can bring a UV flash light and show the radium fluorescence. Adults love UV flash lights.

 10·4 months ago
10·4 months agoI am also quite interested in this. It is not something that keeps me awake at night, and I am not particularly paranoid about it. But I find that working towards answering this question is a fun frame from which to learn about electronics, radio communications, and networking.
Since this appears to be something that is causing you some anxiety, I think it is better if I start by giving you some reassurance in that I have not yet managed to prove that any electronic device is spying on me via a hidden chip. I don’t think it is worth being paranoid about this.
I can explain some things that could be done to test whether a Linux computer spying. I am not suggesting that you try any of this. I am explaining this to you so that you can get some reassurance in the fact that, if devices were spying on us in this manner, it is likely that someone would have noticed by now.
The “spy” chip needs some way to communicate. One way a chip might communicate is via radio waves. So, the first step would be to remove the WiFi and Bluetooth dongles and any other pieces of hardware that may emit radio waves during normal operation. There is a tool called a “Spectrum Analyzer” that can be used to capture the presence of specific radio frequencies. These devices are now relatively affordable, like the tinySA, which can measure the presence of radio frequencies of up to 6 GHz.
One can make a Faraday cage, for example, by wrapping the PC with a copper-nickel coated polyester fabric to isolate the PC from the radio waves that are coming from the environment. The spectrum analyzer antennas can be placed right next to the PC and the device is left to measure continuously over several days. A script can monitor the output and keep a record of any RF signals.
Since phones are small, it is even easier to wrap them in the copper-nickel polyester fabric alongside with the spectrum analyzer antenna to check whether they emit any RF when they are off or in airplane mode with the WiFi and Bluetooth turned off.
What this experiment may allow you to conclude is that the spy chip is not communicating frequently with the external world via radio frequencies, at least not with frequencies <= 6 GHz.
Using frequencies higher 6 GHz for a low-power chip is not going be an effective method of transmitting a signal very far away. The chip could remain hidden and only emit the signal under certain rare conditions, or in response to a trigger. We can’t rule that out with this experiment, but it is unlikely.
A next step would be to test a wired connection. It could be that the spy chip can transmit the data over the internet. One can place a VPN Gateway in between their PC and the router, and use that gateway to route all the traffic to their own server using WireGuard. All network packets that leave through the PC’s ethernet connection can be captured and examined this way using Wireshark or tcpdump.
If one can show that the device is not secretly communicating via RF nor via the internet, I think it is unlikely that the device is spying on them.
You can take a lot of control by using search commands. Here is a list of commands for Google, for example: https://www.lifewire.com/advanced-google-search-3482174
By using commands like these you can narrow down your searches to the point that the impact of SEO is small. You give a much greater weight to the conditions that you have chosen.
It can be a bit of work to write a good search query, but the database that search engines search through is massive, so it makes sense that it would take some work to do this right.
Search engines like google aggregate data from multiple sites. I may want to download a datasheet for an electronic component, find an answer to a technical question, find a language learning course site, or look for museums in my area.
Usually I make specific searches with very specific conditions, so I tend to get few and relevant results. I think search engines have their place.

 3·4 months ago
3·4 months agoI used to it eat a lot of it as a child. But now that I think more about nutrition it is a rare treat for me. I don’t buy it nor keep any at my home, because if I buy it I’ll eat it. If I go out and eat fries I’ll usually eat them with mayonnaise. I do like the taste, especially in egg sandwiches.

 2·4 months ago
2·4 months agoFair enough. I just looked it up and if the scale in this image is correct, I agree that the size of the hole looks small in comparison. I also looked at the security video of the crash itself and it is frustrating how little we can see from it.
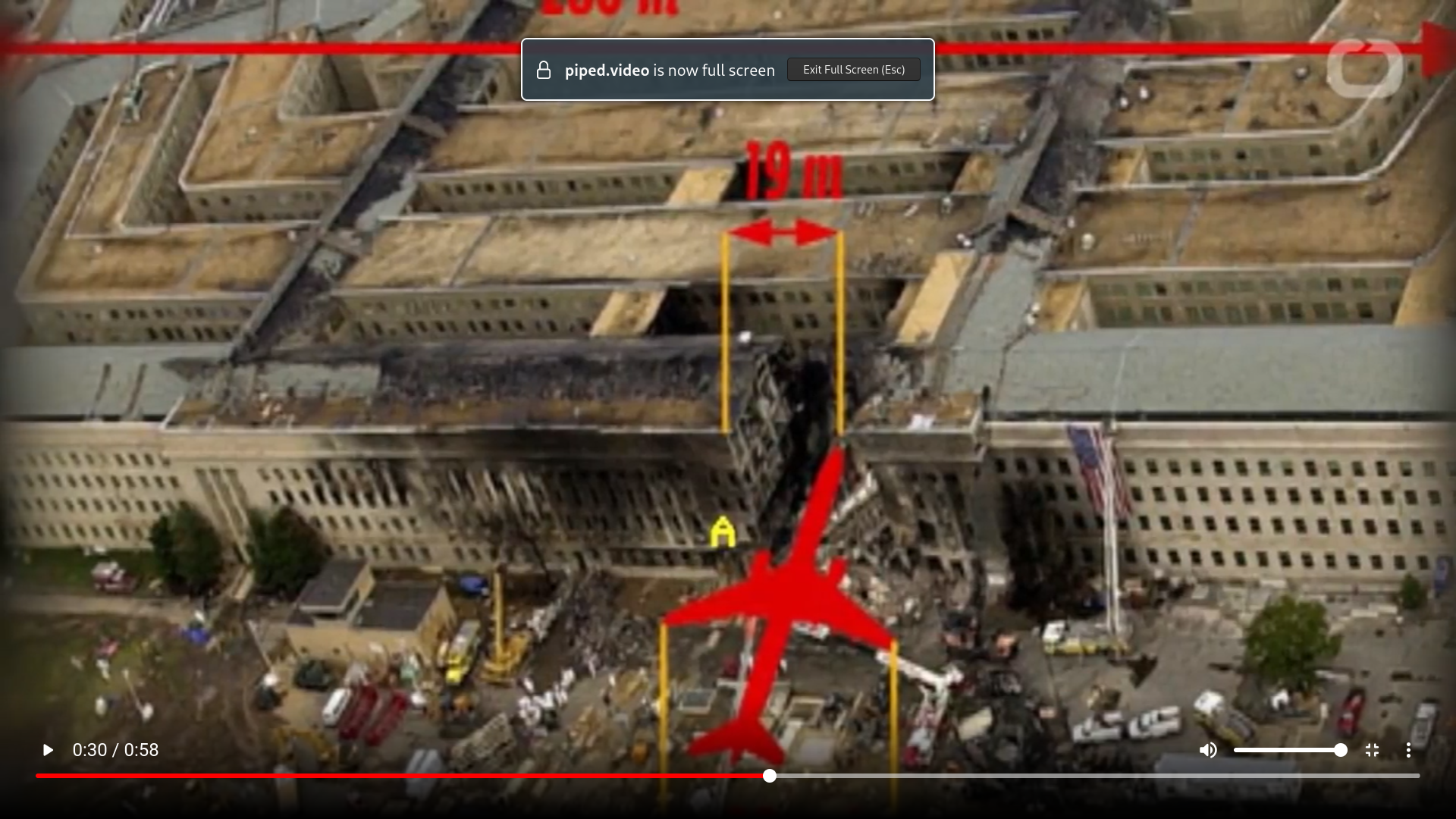
Since this was such an important event and there seems to be a lack of specific pieces of essential evidence - either because of bad luck or because of a cover-up - I understand the skepticism. And I am not a fan of blindly believing any official narrative. But, without any context, if I see that photo and someone tells me that a plane crashed into that building, I would find it probable simply because the shape is so similar to the photo of the Bijlmer accident that I’m familiar with. A plane crash seems to me like a very chaotic process, so I don’t have a good expectation of what the damage should look like.
Maybe I’ll look for a pentagon crash documentary some time.

 1·4 months ago
1·4 months agoI don’t have much of an opinion on this topic, I haven’t really looked into it.
But as soon as I saw this image, the El Al Flight 1862 which crashed in the Bijlmer in Amsterdam in 1992 immediately came to mind. The shape of the hole is very similar!

This image shows the likely position of the Bijlmer plane during the crash:

The image you posted of the Pentagon seems to me consistent with what I have seen of the Bijlmer accident, and so the shape of the hole and the absence of wings in the photo does not persuade me personally that no plane was involved.
Works flawlessly now :D Thank you again for your hard work!!
Thank you!!! Very happy about the moderation tools!
There is a problem opening community pages. I checked and the bug was introduced with this version.

 2·5 months ago
2·5 months agoI am not sure as I did not test this one. Maybe you can go in person and get a worker to get you access to the kiosk through your account to print the card. It is one of those massive chains with gyms in every corner. I think that by now they rely on their digital infrastructure and many of their workers are not trained to handle uncommon situations. At least I get that from some of my experiences, but I could be wrong, maybe if I would have called them could have helped me with this. It was just easier to get the app into my old phone, print a card, delete the app.

 3·5 months ago
3·5 months agoI think that it works, but for it to work you need to enable Google Play services. From what I understand, this is done in a sandboxed manner simulating a fake identity, so it is possible to do this while isolating Google from your phone to an extent. But I think that WhatsApp is in itself problematic and one of the direct offenders that I want to avoid, regardless of its reliance on Google Play services, and so I have not gone through this effort myself.









I did not know of the term “open washing” before reading this article. Unfortunately it does seem like the pending EU legislation on AI has created a strong incentive for companies to do their best to dilute the term and benefit from the regulations.
There are some paragraphs in the article that illustrate the point nicely:
Thank you for pointing out Grayjay, I had not heard of it. I will look into it.